You naturally want to minimize risks and avoid cost overruns before signing a long-term contract for a new ERP system or any new system. Your prospective vendor also wants to minimize risk but is usually not able to do more than give an implementation estimate based on assumptions about scope, roles, and responsibilities. These assumptions could be fairly accurate, but could also be way off, which could lead to surprises and costly change orders. Neither you nor the vendor wants this to happen. For the vendor, you could turn into an unhappy client who cannot be referenced, or even worse, one who wants to abandon the project. Today, with most licenses sold as Software as a Service with annual fees, the vendor would lose a significant revenue stream. One solution is a paid-for Business Needs Analysis (BNA).
What is a BNA? What does BNA stand for? BNA meaning?
BNA stands for Business Needs Analysis and is a systematic process of identifying and evaluating the needs of a business to determine the best way to address these needs. It involves gathering detailed information about the business environment, processes, and requirements to ensure that the ERP implementation is tailored to meet these needs effectively. Understanding the BNA meaning is essential, as it helps prevent scope mismatches and surprises later in the project.
Although the vendors charge for their time to complete the BNA, they would be charging for this time during the implementation anyway, and by doing the work upfront, they can integrate the risky parts into the implementation contract and reduce the likelihood of surprises.
Why is BNA important? Focus on Critical Requirements
It is assumed that a lot of work has been done already in defining requirements and attending demonstrations. Therefore, you don’t want to start all over again. Instead, you should just focus on critical requirements, which are not available out-of-the-box from the vendor and seem to require customization. Identify the requirements that are the most challenging and/or unique and make sure the vendors understand them so they can figure out how to handle them in detail before the contract is finalized. Understanding the BNA meaning helps vendors and clients navigate these challenges effectively.
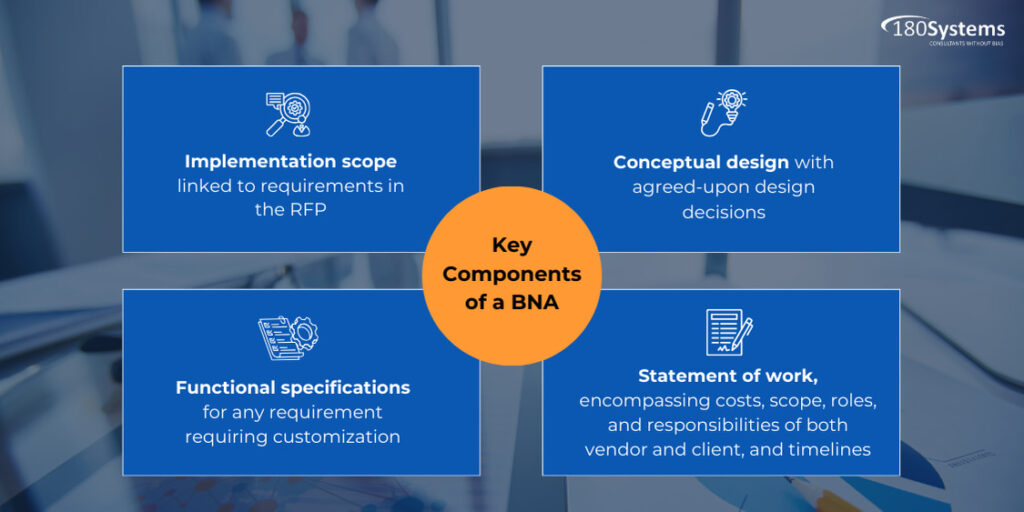
Key Components of a BNA
A well-executed BNA should encompass the following:
- Implementation scope linked to requirements in the RFP
- Conceptual design with agreed-upon design decisions
- Functional specifications for any requirement requiring customization
- Statement of work, encompassing costs, scope, roles, and responsibilities of both vendor and client, and timelines.
Addressing Vendor Resistance to BNA
Vendors may resist engaging in a BNA, preferring to close deals swiftly or hesitating to allocate resources to a non-contractual client. However, a high-risk scenario benefits both vendor and client through the BNA approach, ensuring mutual protection.
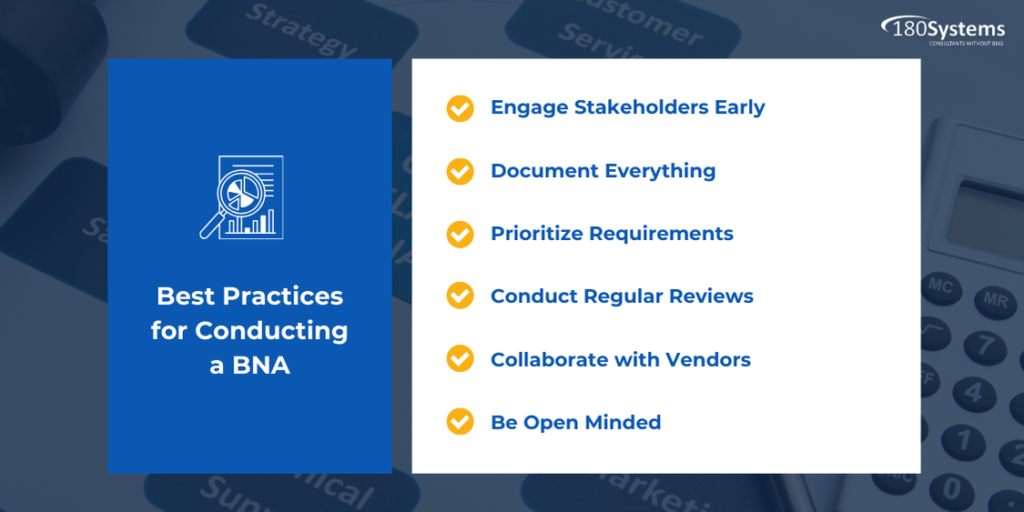
Best Practices for Conducting a BNA
- Engage Stakeholders Early: Involve key stakeholders from the beginning to ensure their needs and expectations are understood.
- Document Everything: Keep detailed records of all requirements, decisions, and changes to maintain clarity and transparency.
- Prioritize Requirements: Focus on the most critical requirements first to ensure they are addressed effectively.
- Conduct Regular Reviews: Regularly review and update the BNA to reflect any changes in business needs or circumstances.
- Collaborate with Vendors: Work closely with vendors to ensure they fully understand the business requirements and can provide accurate estimates and solutions.
- Be Open Minded: The vendor may not be able to meet the exact requirement but could have an alternate method that does not involve customization. It is preferable to avoid customizations wherever possible. They can be costly to implement and to maintain over the years.
Summary
Ideally, you didn’t need to do a Business Needs Analysis as most of your requirements are met by the new system. But if there are significant gaps for critical requirements, then a BNA will reduce the risks but also extend the go-live date. If the risks are high and you’re ok to delay the go-live date, then a Business Needs Analysis is recommended.